Slack plan: Business+ or Enterprise Grid required.
Prefer a managed solution? Tightknit offers a hosted SSO integration that handles identity provider configuration, membership verification, and error handling out of the box, no Auth0 or third-party IDP required. Contact [email protected] to learn more.
Prerequisites
- A Slack workspace on the Business+ or Enterprise plan
- An Auth0 tenant (free tier works)
This guide uses Auth0 as the identity provider. The same pattern applies to other IDPs that support SAML 2.0.
Setting up Slack SSO
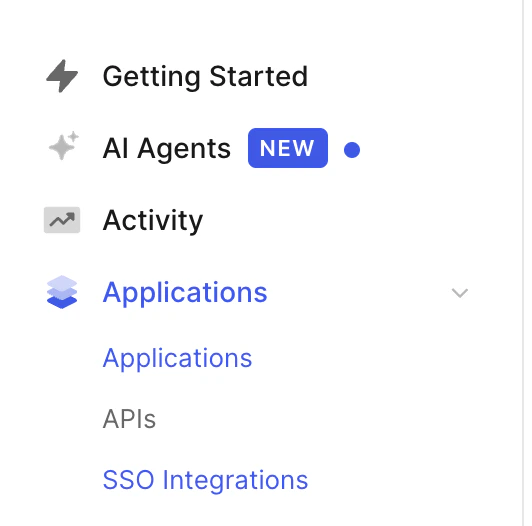
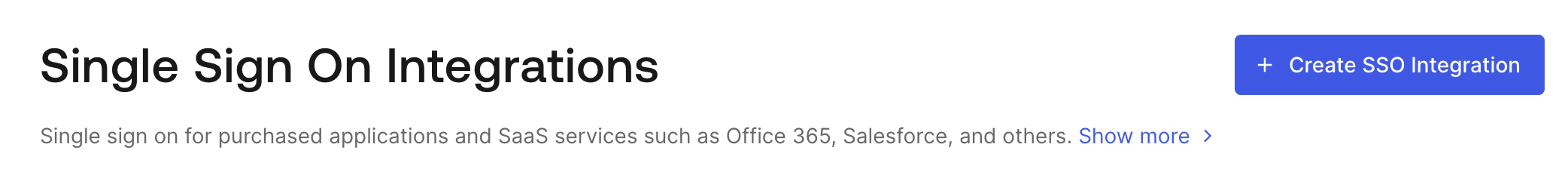
In Auth0
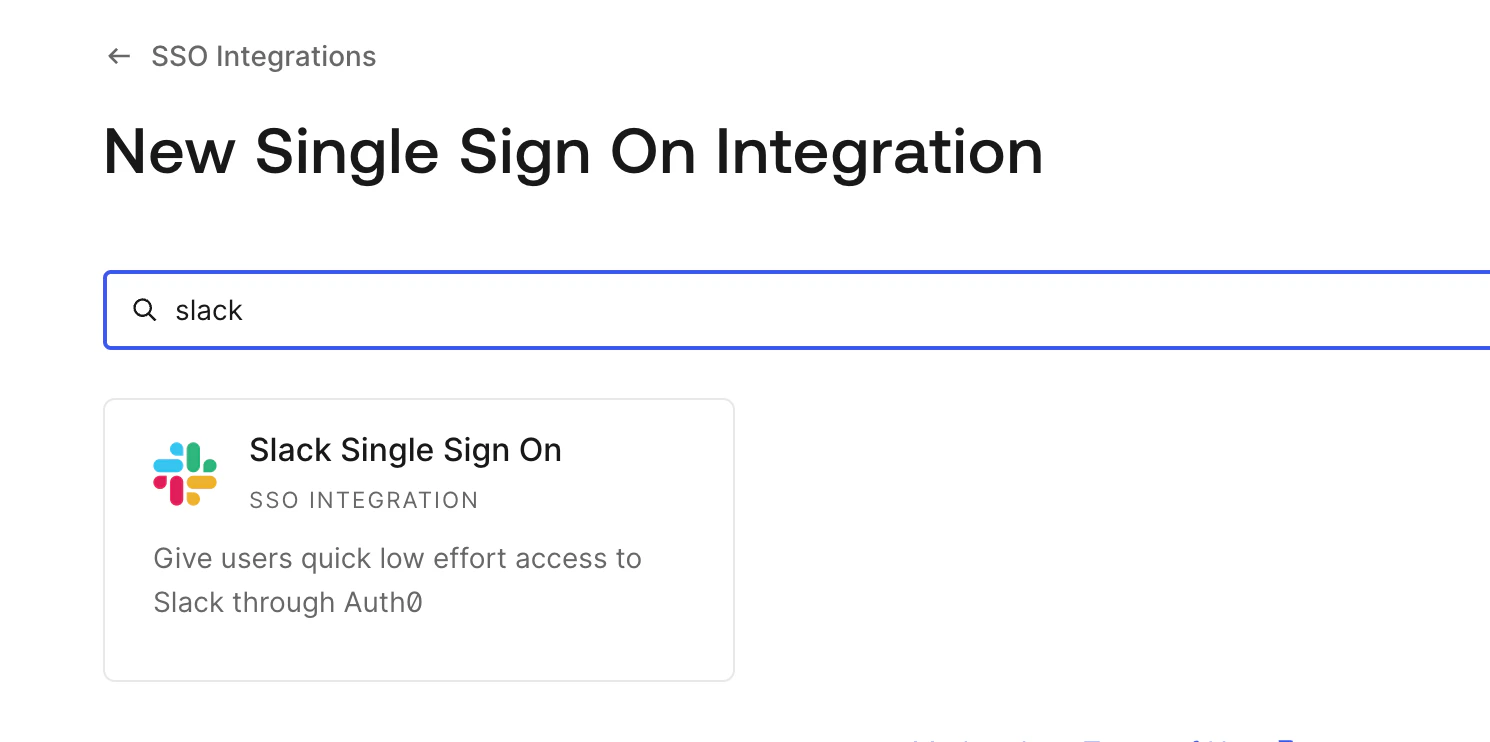
Auth0 provides a pre-built Slack SSO integration that handles the SAML configuration for you.Name it and save
Enter a Name (e.g. 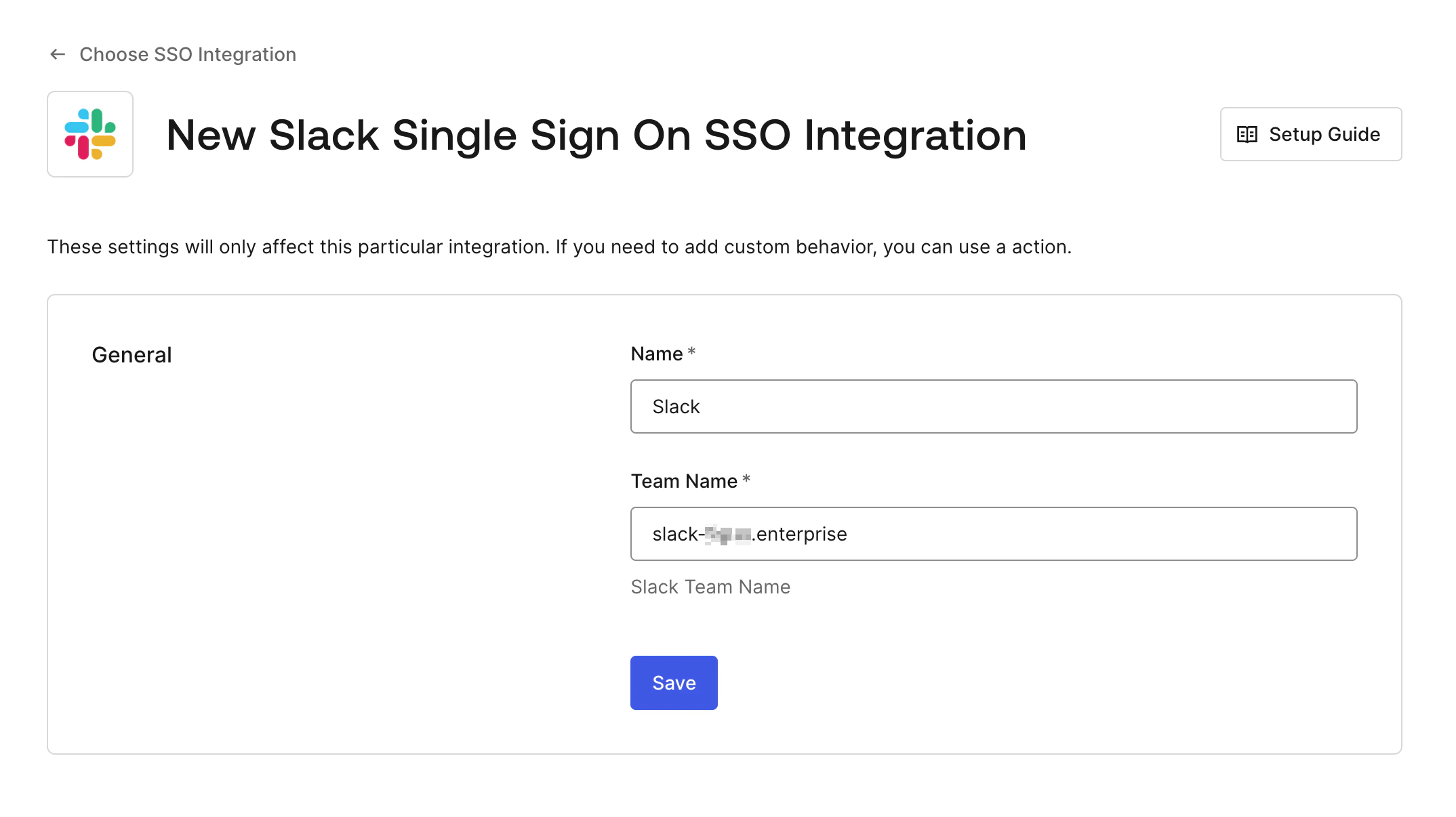
Slack) and your Slack Team Name, then click Save:- Business+: your workspace URL slug, e.g.
your-workspace(fromyour-workspace.slack.com) - Enterprise Grid: your Grid org slug with the
.enterprisesuffix, e.g.your-workspace.enterprise
In Slack
Open Slack SSO Settings
In Slack, go to Settings & administration > Workspace settings > Authentication > SSO Settings (or your Org-level SSO page on Enterprise Grid).
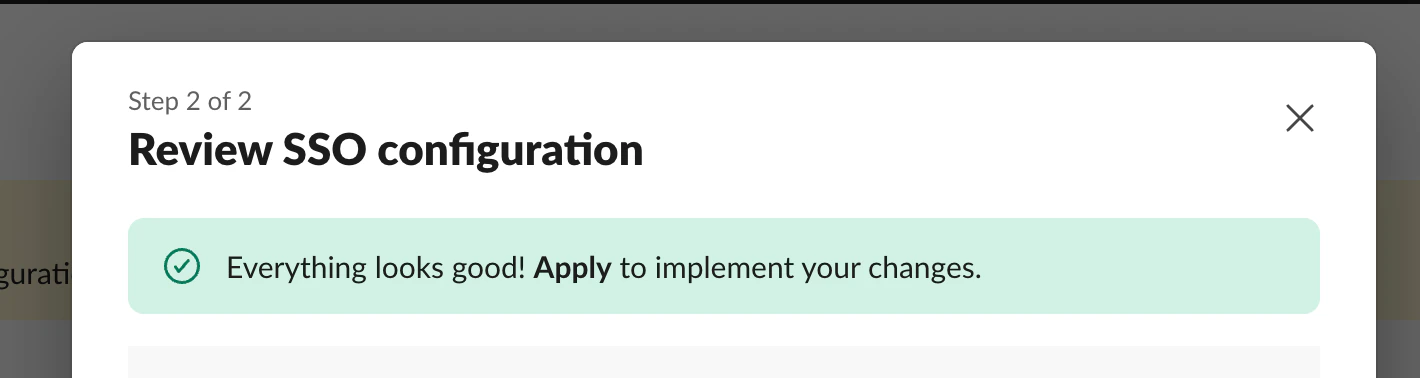
Fill in the SAML fields
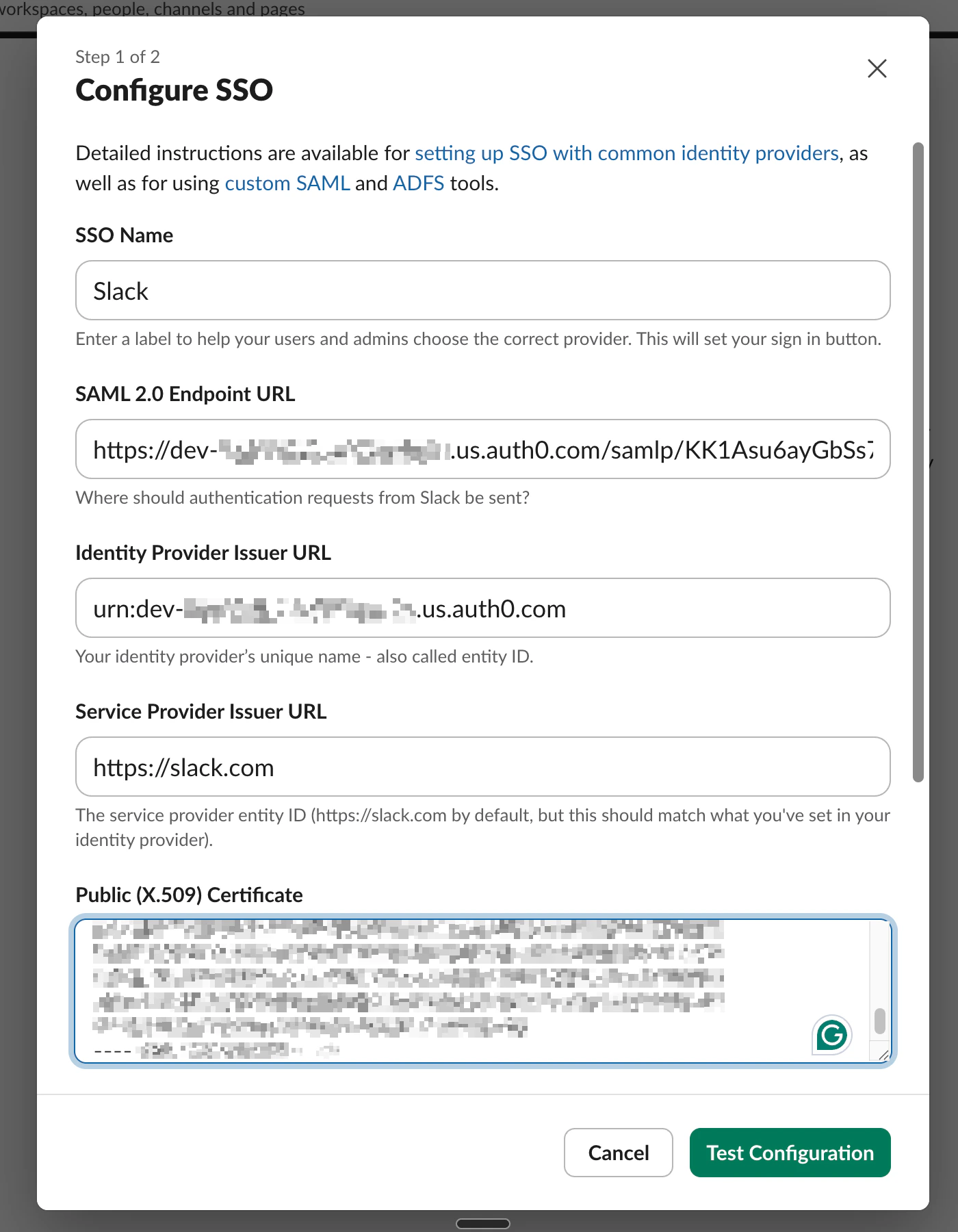
Click Configure. In the SSO dialog that opens, fill in the SAML fields at the top using values from your Auth0 SSO integration:
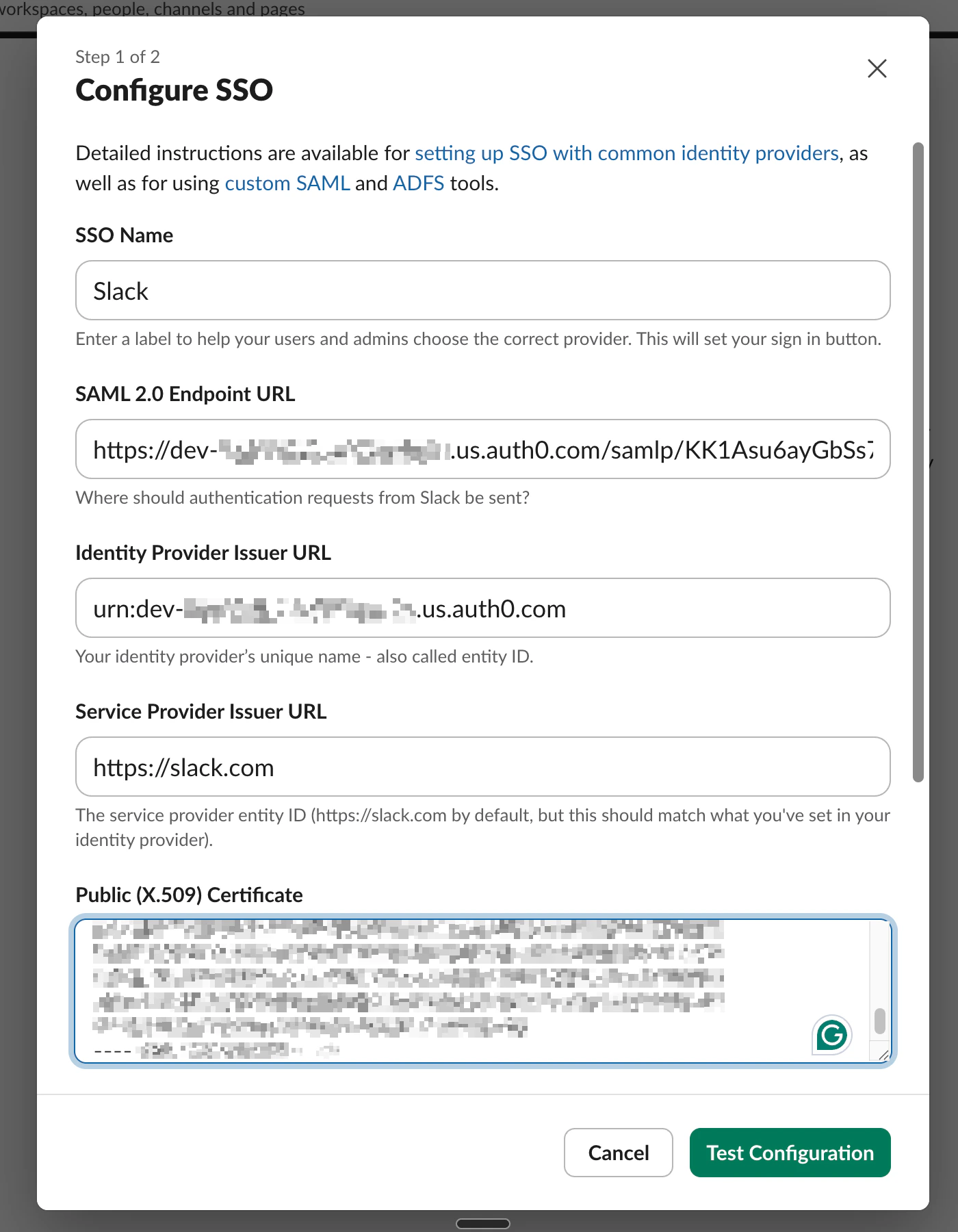
| Slack field | Auth0 value |
|---|---|
| SSO Name | A label for the sign-in button, e.g. Auth0 |
| SAML 2.0 Endpoint URL | The Auth0 SAML endpoint, e.g. https://your-tenant.us.auth0.com/samlp/... |
| Identity Provider Issuer URL | The Auth0 issuer URN, e.g. urn:dev-xxxxx.us.auth0.com |
| Service Provider Issuer URL | https://slack.com (default) |
| Public (X.509) Certificate | Copy the full certificate from Auth0 |
Set signing and authentication context
Scroll down in the same dialog and set: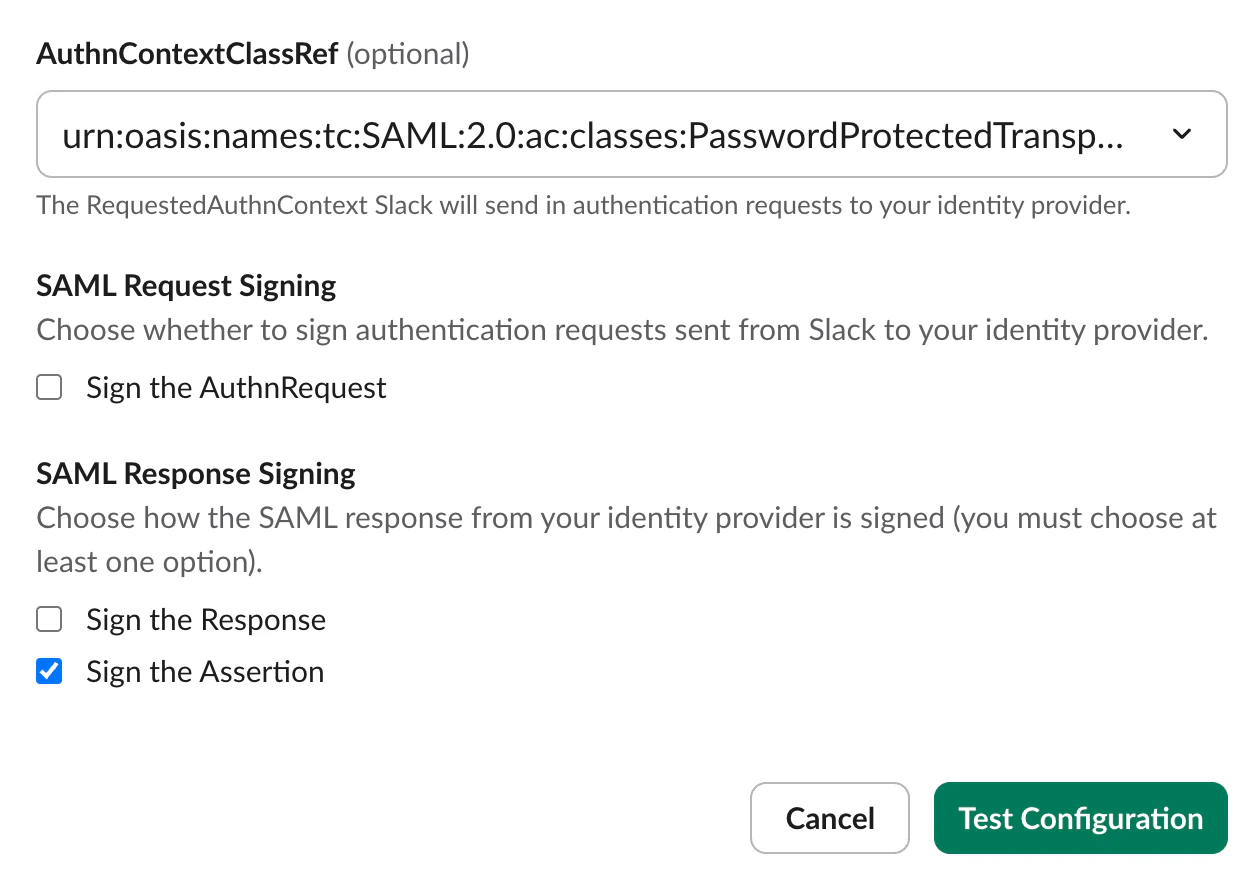
- AuthnContextClassRef: Leave as the default (
urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport) - SAML Request Signing: Leave unchecked unless your IDP requires signed requests
- SAML Response Signing: Check Sign the Assertion (at least one signing option is required)
Signing the SAML response (optional)
Signing the assertion alone is secure for most deployments. The assertion is the part of the SAML payload that carries the user’s identity and authentication claims, so signing it protects the data Slack actually trusts. Signing the outer response adds a second signature over envelope metadata (issuer, destination,
InResponseTo) and is defense-in-depth, not a prerequisite — the default Auth0 Slack SSO integration signs only the assertion for this reason.Follow the steps below only if your security team explicitly requires signResponse (for example, to satisfy an internal SAML hardening policy or a compliance control). Doing so requires replacing the pre-built SSO integration with a custom SAML application.Create a custom SAML application
In Auth0, go to Applications > Applications and create a Regular Web Application.
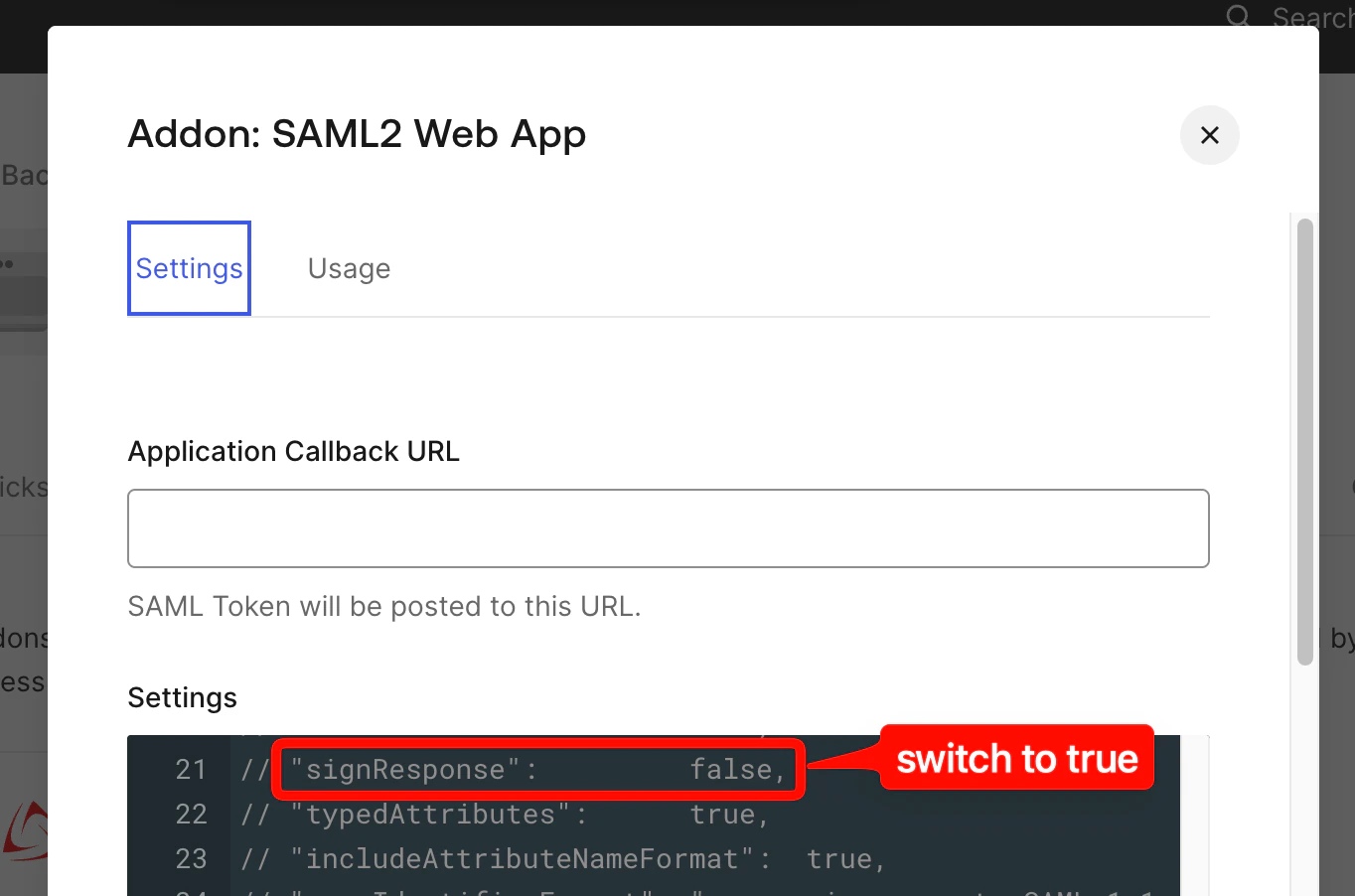
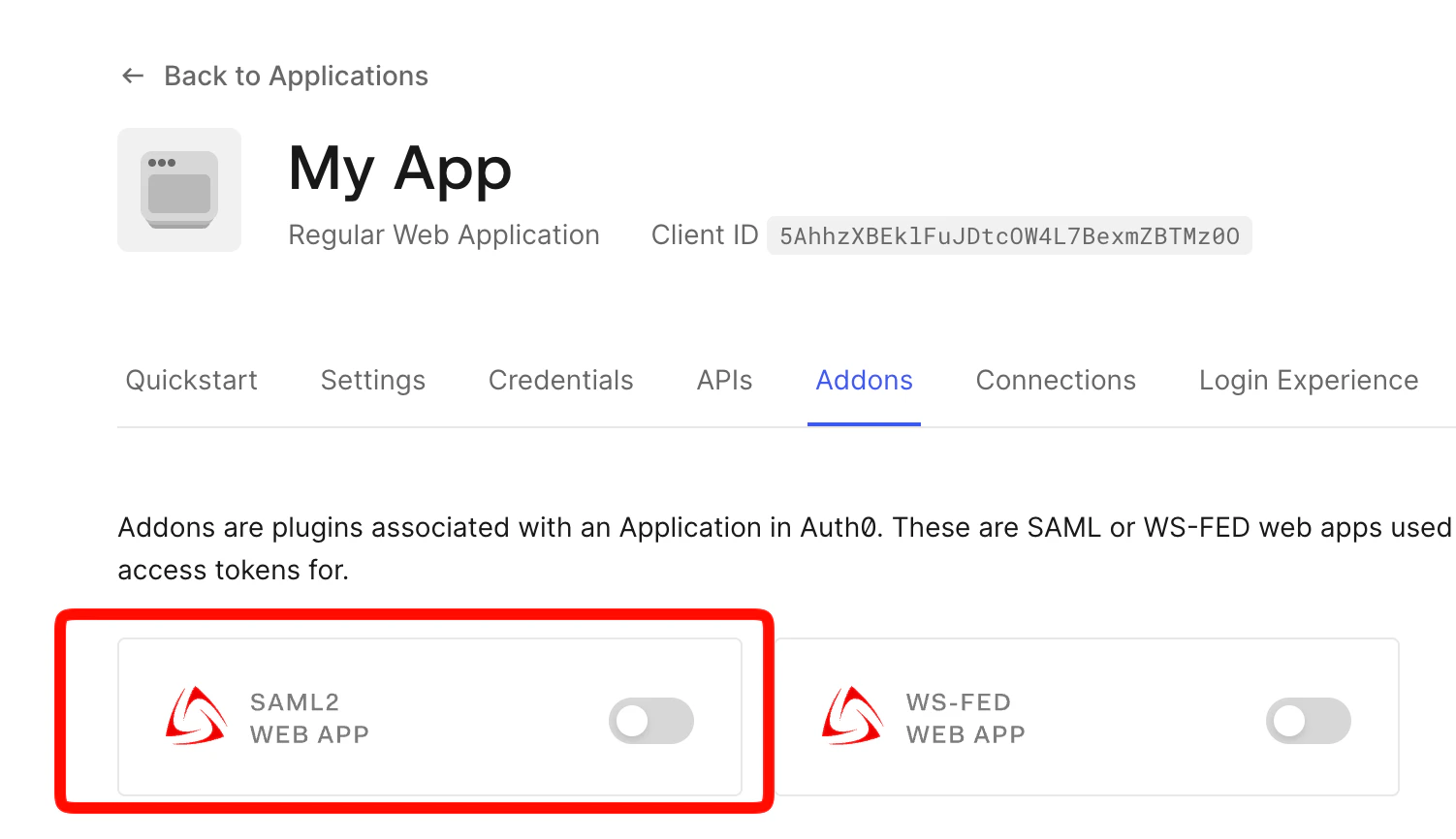
Enable the SAML2 Web App addon
Open the application, go to the Addons tab, and enable the SAML2 Web App addon.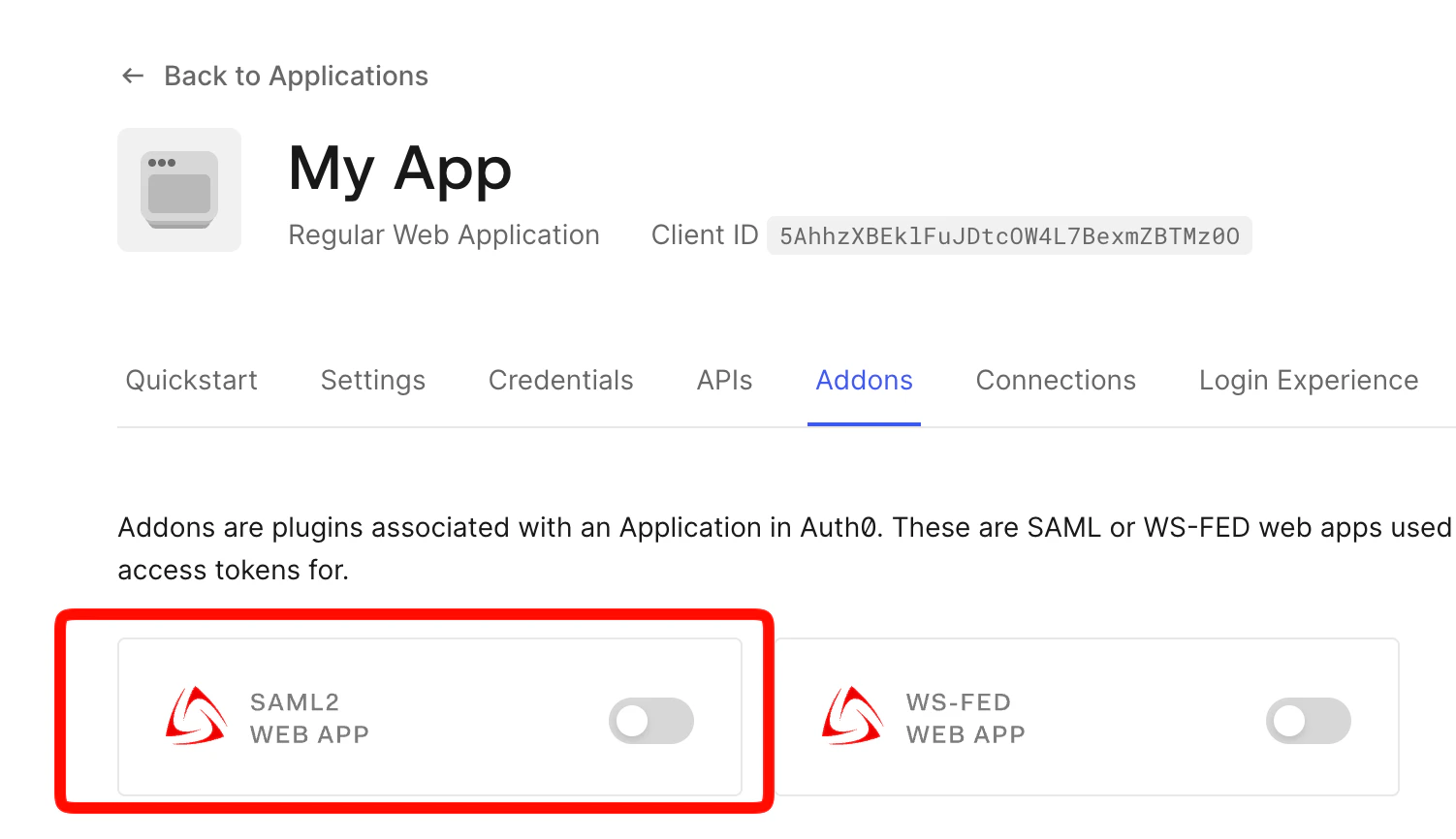
Use the new endpoint in Slack
Use the SAML endpoint URL and certificate from this custom application (instead of the SSO integration) when filling in the Slack SSO dialog in the In Slack section above.
Verifying Tightknit community membership (optional)
If you use a social connection (Google, Microsoft, etc.) as the login method in Auth0, anyone with a valid social account can authenticate, even if they are not a member of your community. The steps below add a post-login check that verifies membership via the Tightknit API before granting access.Additional prerequisites
- A Google (or other) social connection enabled in Auth0
- A Tightknit API key for your community
In Tightknit Studio
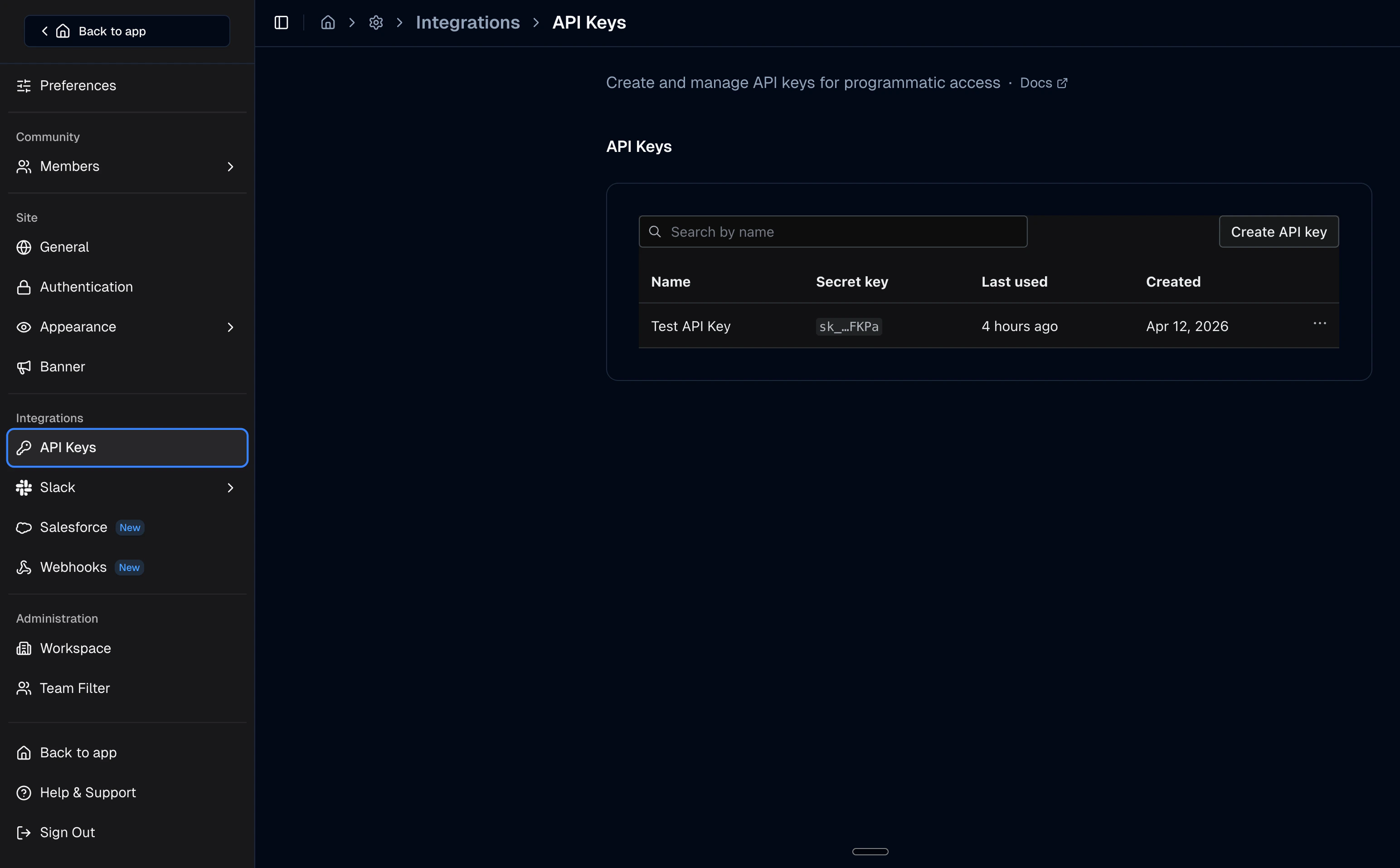
Get your Tightknit API key
Open Tightknit Studio, go to Integrations > API Keys, and create or copy an existing key.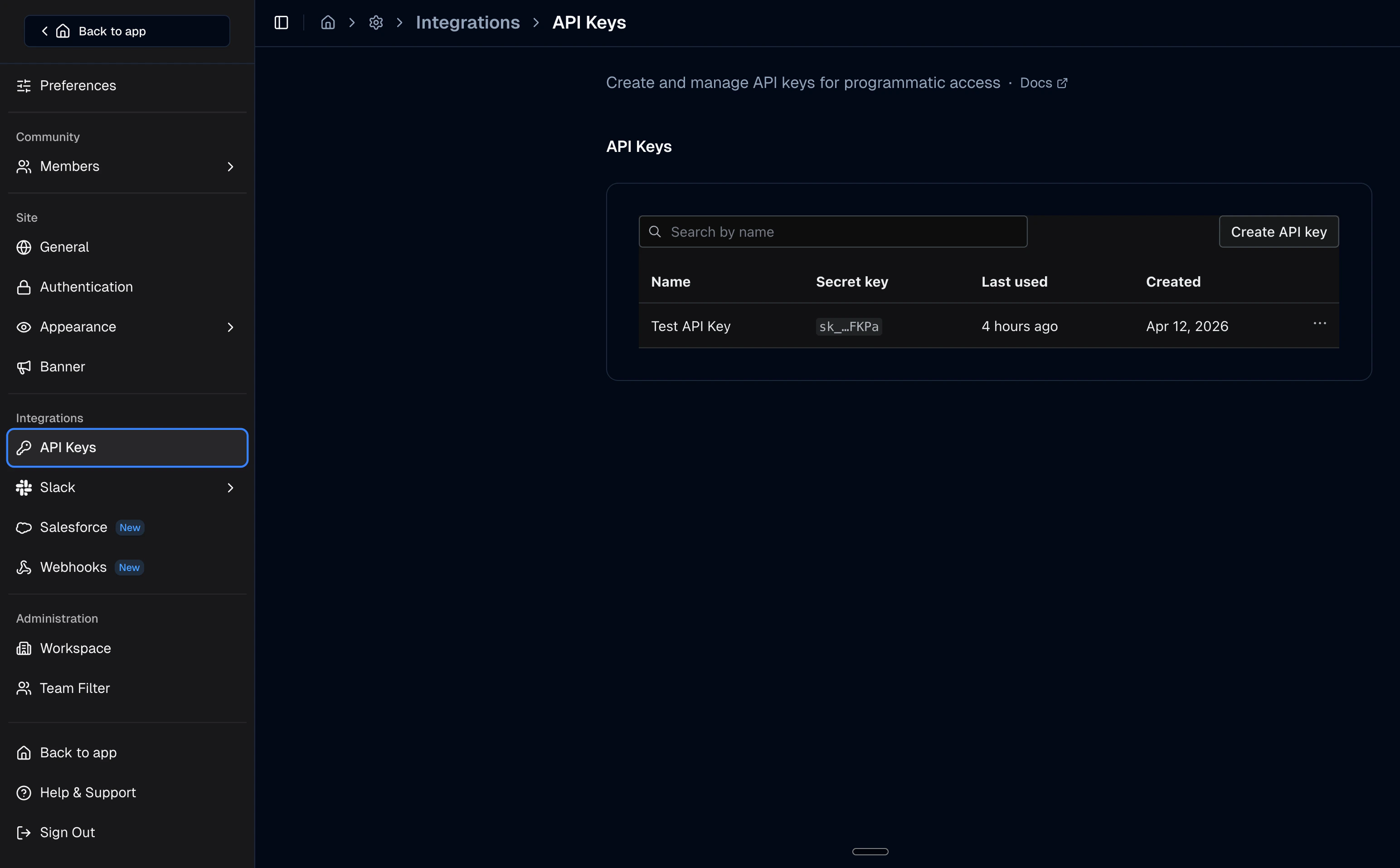
In Auth0
Why is this needed? If your Auth0 tenant uses a social connection (Google, Microsoft, etc.) as the login method for your SAML application, anyone with a valid social account can authenticate, even if they are not a member of your community. IDPs cannot reject users before the social login completes, so a post-login check is required to verify membership. Without it, non-members see a broken Slack authentication failure instead of a clear error message.
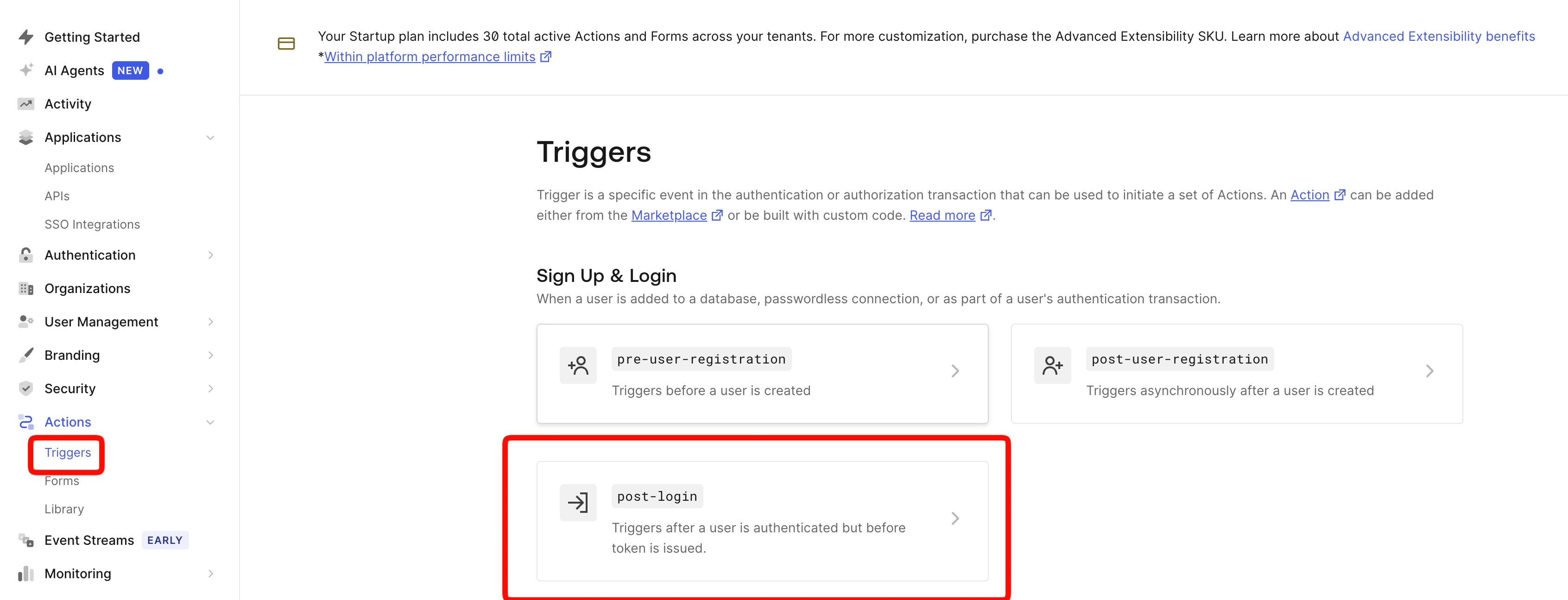
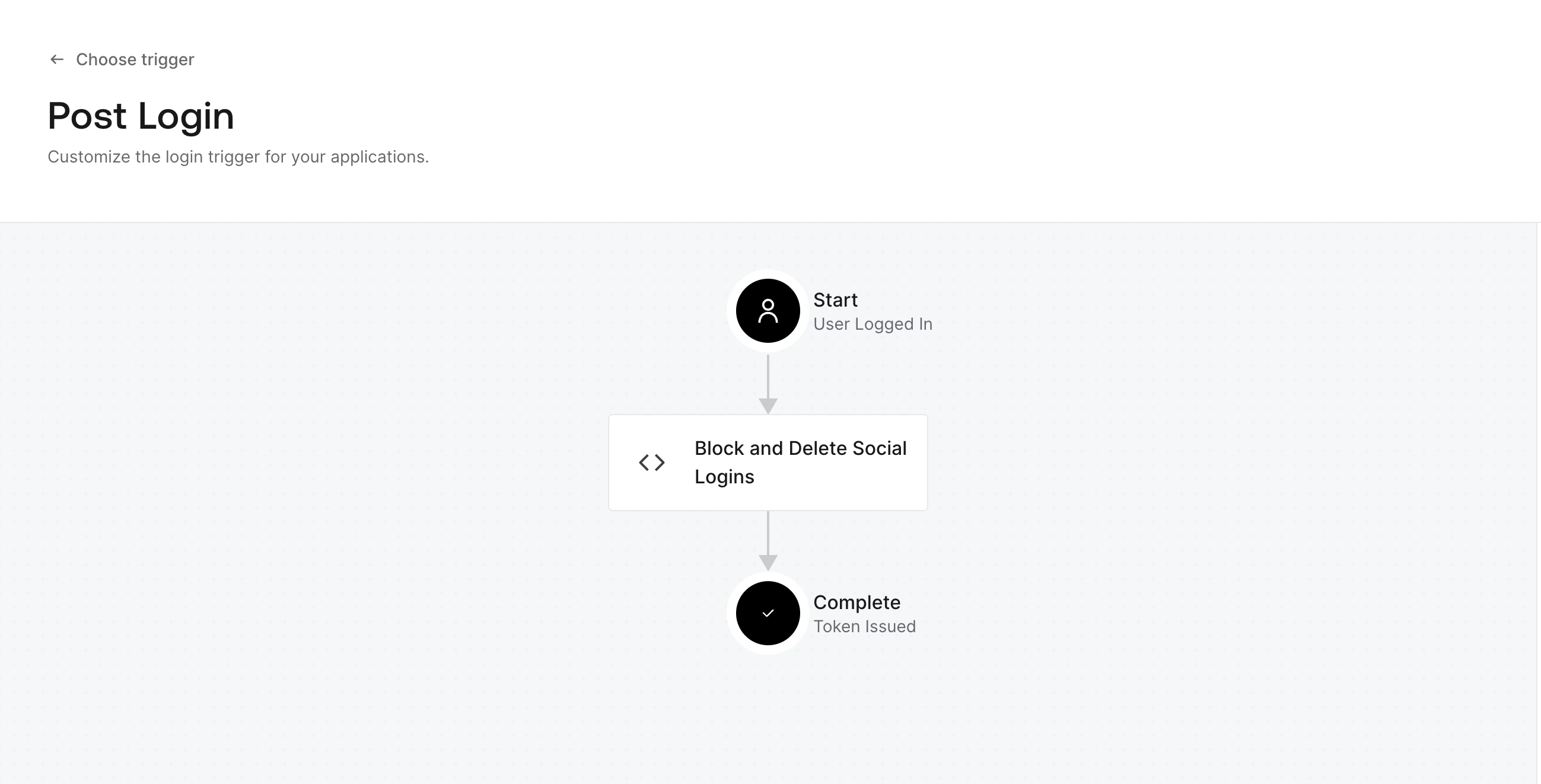
Create the post-login action
In the Auth0 Dashboard, go to Actions > Library > Build Custom. Name it Tightknit Membership Check, select the Login / Post Login trigger, and paste the code below.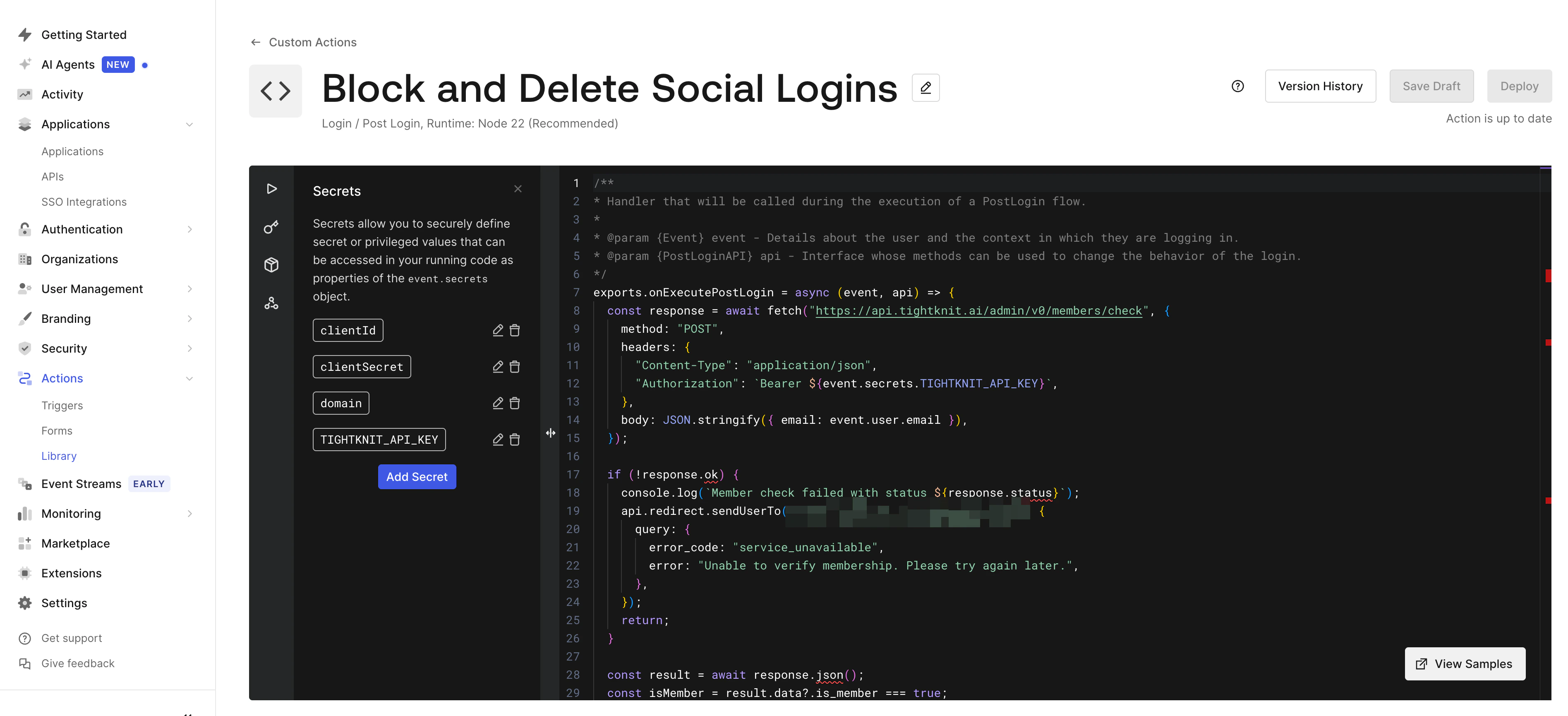
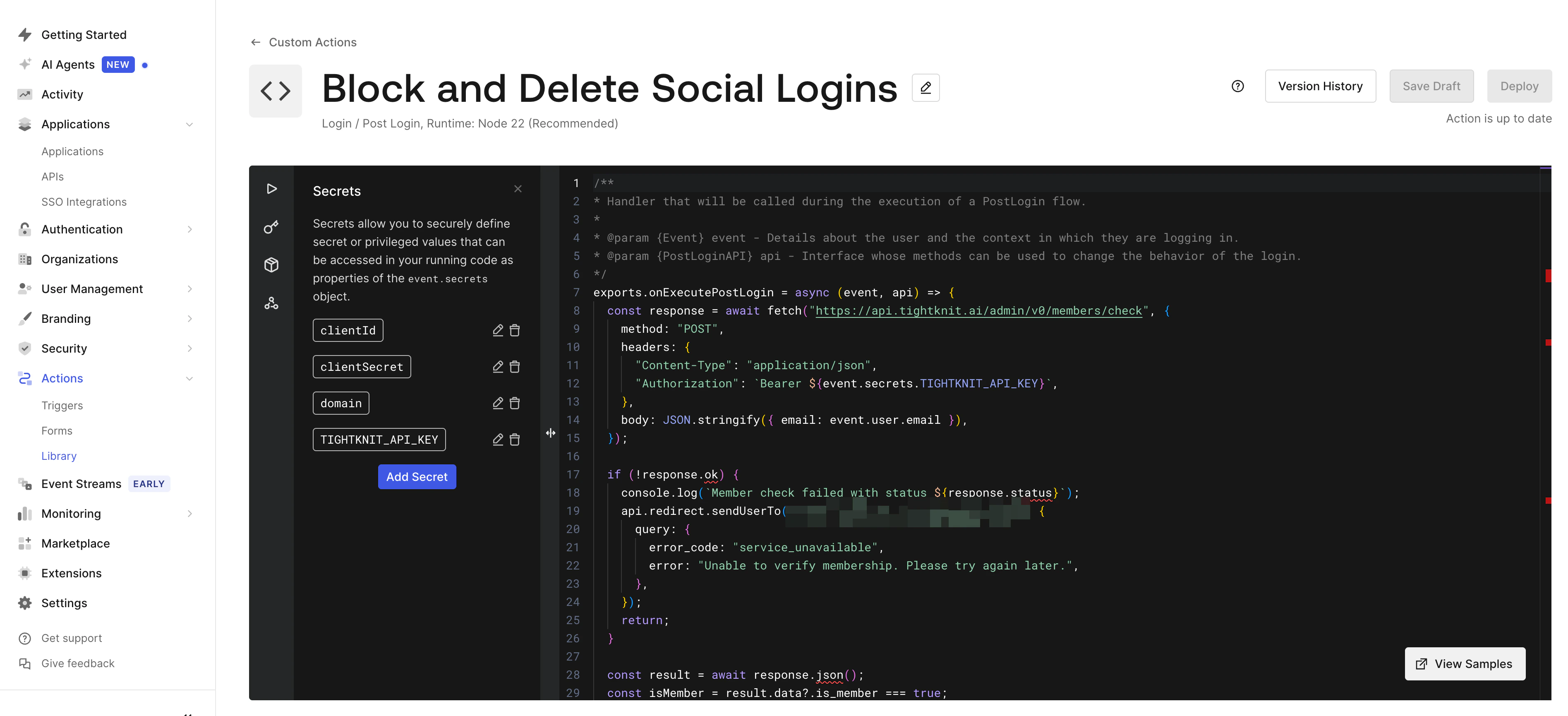
Auth0 Action
Add secrets to the action
In the action editor, click the lock icon (Secrets) and add:
| Secret | Value |
|---|---|
TIGHTKNIT_API_KEY | Your Tightknit API key from the previous section |
domain | Your Auth0 tenant domain, e.g. your-tenant.us.auth0.com |
clientId | Client ID of an Auth0 M2M app authorized for the Management API |
clientSecret | Client secret of that M2M app |
Force account selection (optional)
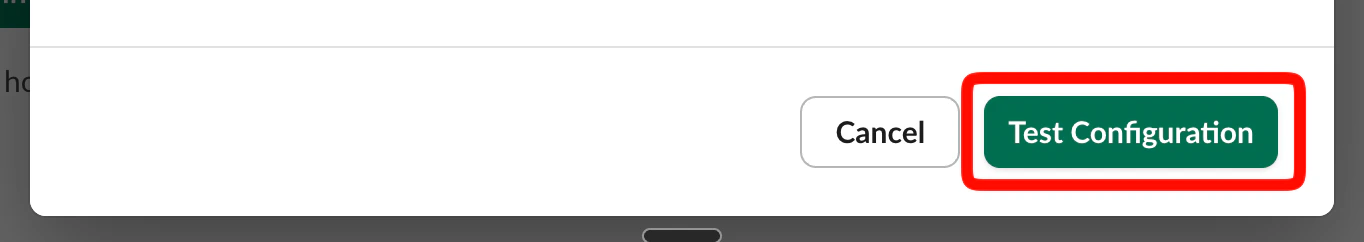
By default, Auth0 may skip the login page using a cached session, and Google may auto-select the last used account. To force users to choose every time, run these one-time Management API calls. Get a Management API token from Applications > APIs > Auth0 Management API > API Explorer.Test
Sign in as a member
Use Slack SSO with an email that belongs to an active community member. You should be logged into Slack.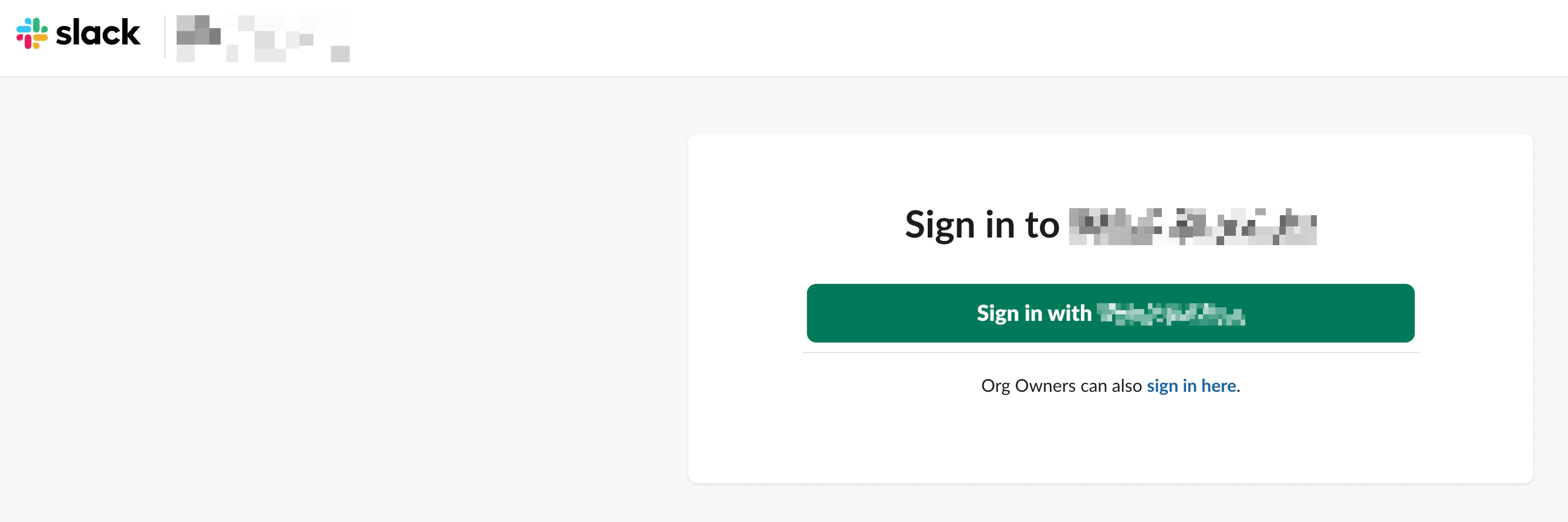
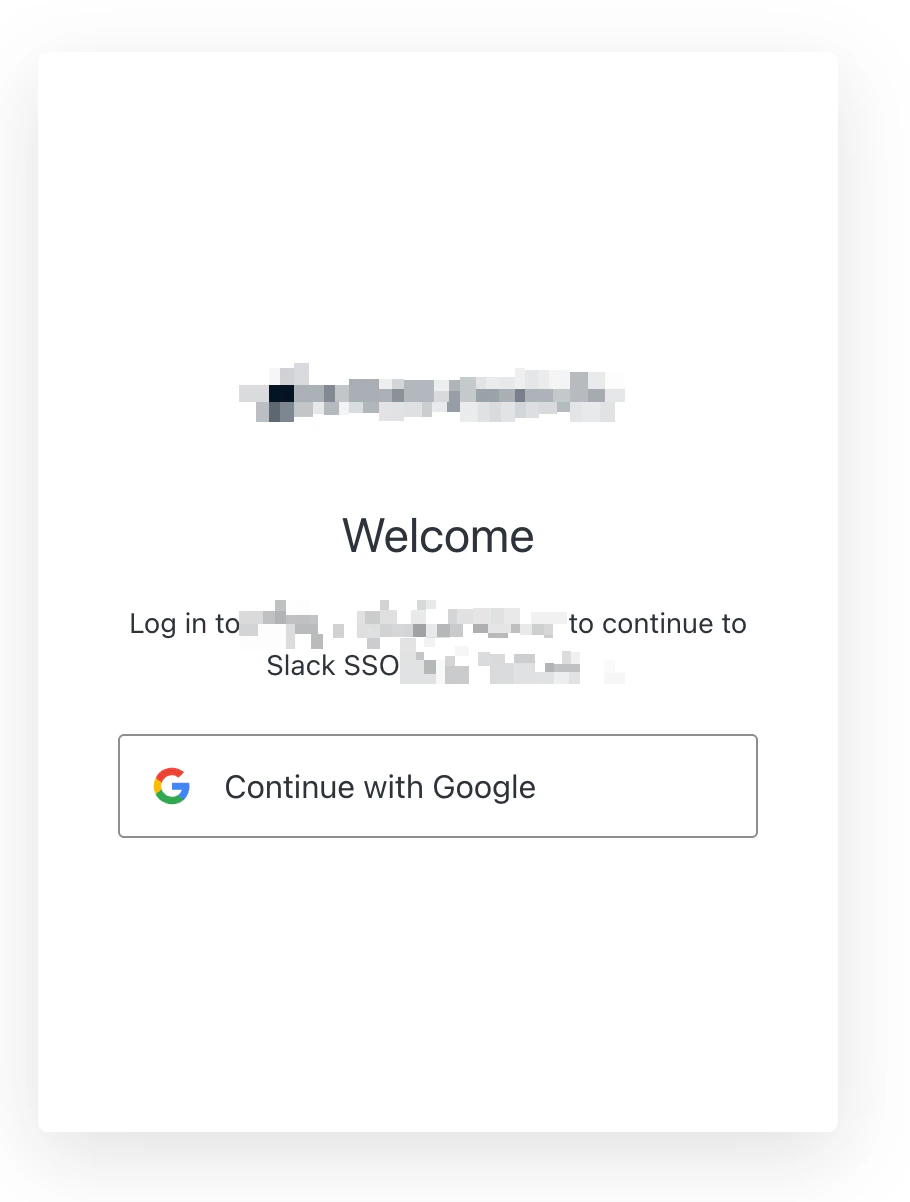
Sign in as a non-member
Use an email that is not in your community. You should be redirected to your login page with the message “An account with this email address does not exist.”
Error codes
When the action redirects to your login page, theerror query parameter tells the page which message to display.
| Code | Message |
|---|---|
member_not_found | An account with this email address does not exist. |
account_deactivated | Your account has been deactivated. Please contact your administrator. |
account_forgotten | Your account is no longer available. Please contact your administrator. |
service_unavailable | Unable to verify your account at this time. Please try again later. |
Troubleshooting
Slack shows a broken error page
Verify the action usesapi.redirect.sendUserTo() and not api.access.deny(). The deny() method sends a failed SAML response that Slack cannot display.
Users are auto-logged in without choosing an account
Run thesso_disabled and upstream_params commands from Force account selection.
Member check returns 401 or 403
Verify theTIGHTKNIT_API_KEY secret is correct. Generate a new key from Studio > Integrations > API Keys if needed.